
You are under LOI on a $10M revenue construction company. Fifteen employees, three states, solid DSCR. Your QoE came back clean. Then someone runs a technology assessment and the results look like most small businesses: no backup on any system, no cyber insurance, outdated server infrastructure, and a few email accounts that appear to have been compromised without anyone noticing.
Not unusual. Not a deal-breaker. But not something you want to discover in month three of ownership when a ransomware attack takes down operations and there is nothing to restore from.
A Quality of Technology (QoT) report does for IT infrastructure what a QoE does for EBITDA: it separates what the seller says from what the evidence shows. It scans the network, audits the software, tests the security posture, and hands you a findings register with severity ratings and dollar estimates you can take to the negotiating table.
Most buyers skip it. The ones who don't tend to find things worth knowing about before they close.
What a QoT Report Actually Does
A QoT assessment evaluates the full technology environment of the business you are acquiring. Not what the seller describes. What the scan reveals.
The assessment typically covers five areas:
Asset inventory and infrastructure. What servers, endpoints, network devices, and cloud applications actually exist? What condition are they in? Are any running end-of-life operating systems? Is the hardware about to fail?
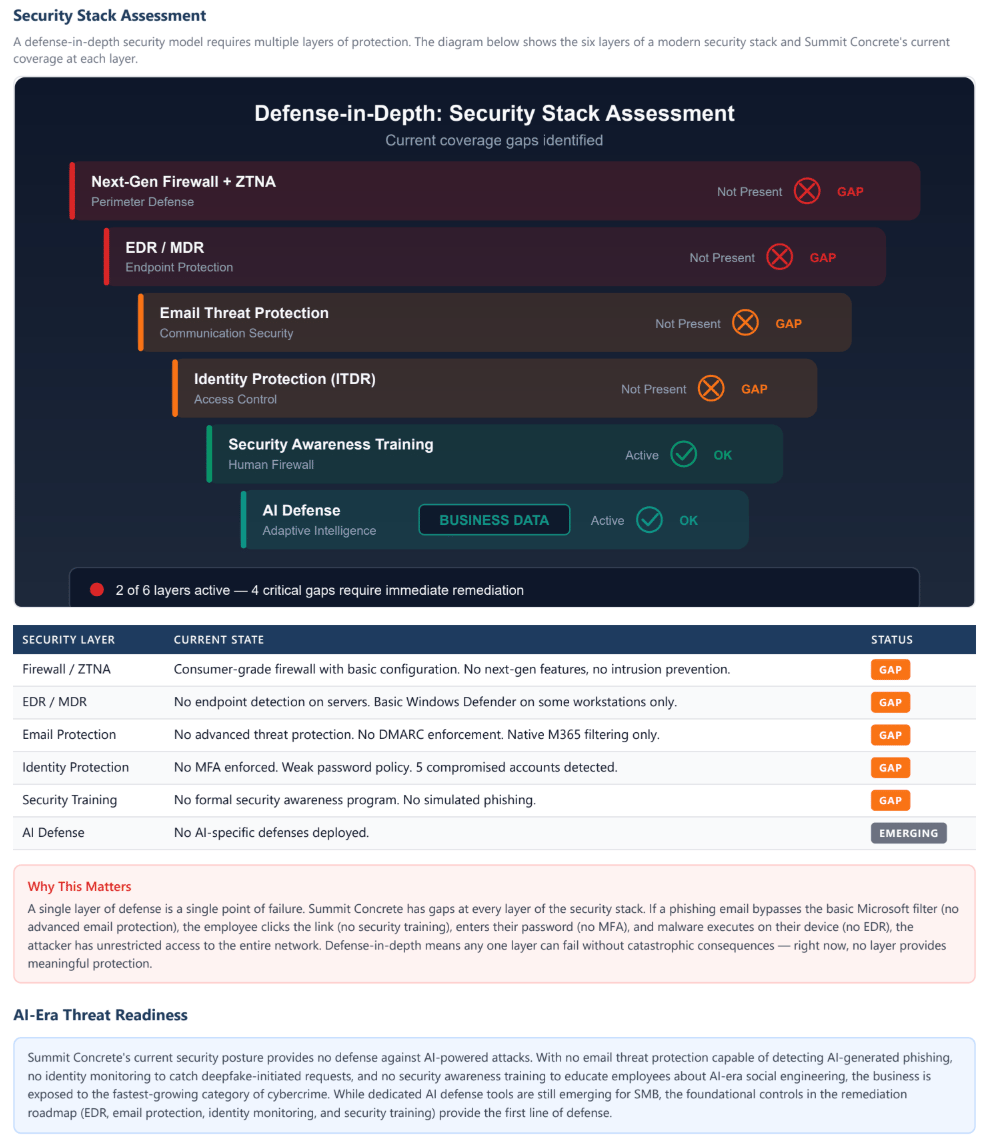
Cybersecurity posture. Is there endpoint detection on the servers? Is multi-factor authentication enforced? Are there active compromises in the email system? How many unpatched vulnerabilities exist across the network? What percentage of Microsoft 365 security checks are passing?
Data protection and backup. If a ransomware attack hit tomorrow, could the business recover? Is there backup coverage on servers, endpoints, and cloud applications? Is any of it tested?
Compliance and licensing. Is the business aligned with any recognized security framework (CIS, NIST)? Are software licenses properly assigned and transferable? Does the company have a privacy policy? Is it compliant enough to qualify for cyber insurance at reasonable rates?
Scalability and technical debt. Can the technology support growth post-close? Is there a single point of failure (one person who knows how the network works)? Are there undocumented custom applications that will be expensive to maintain or replace?
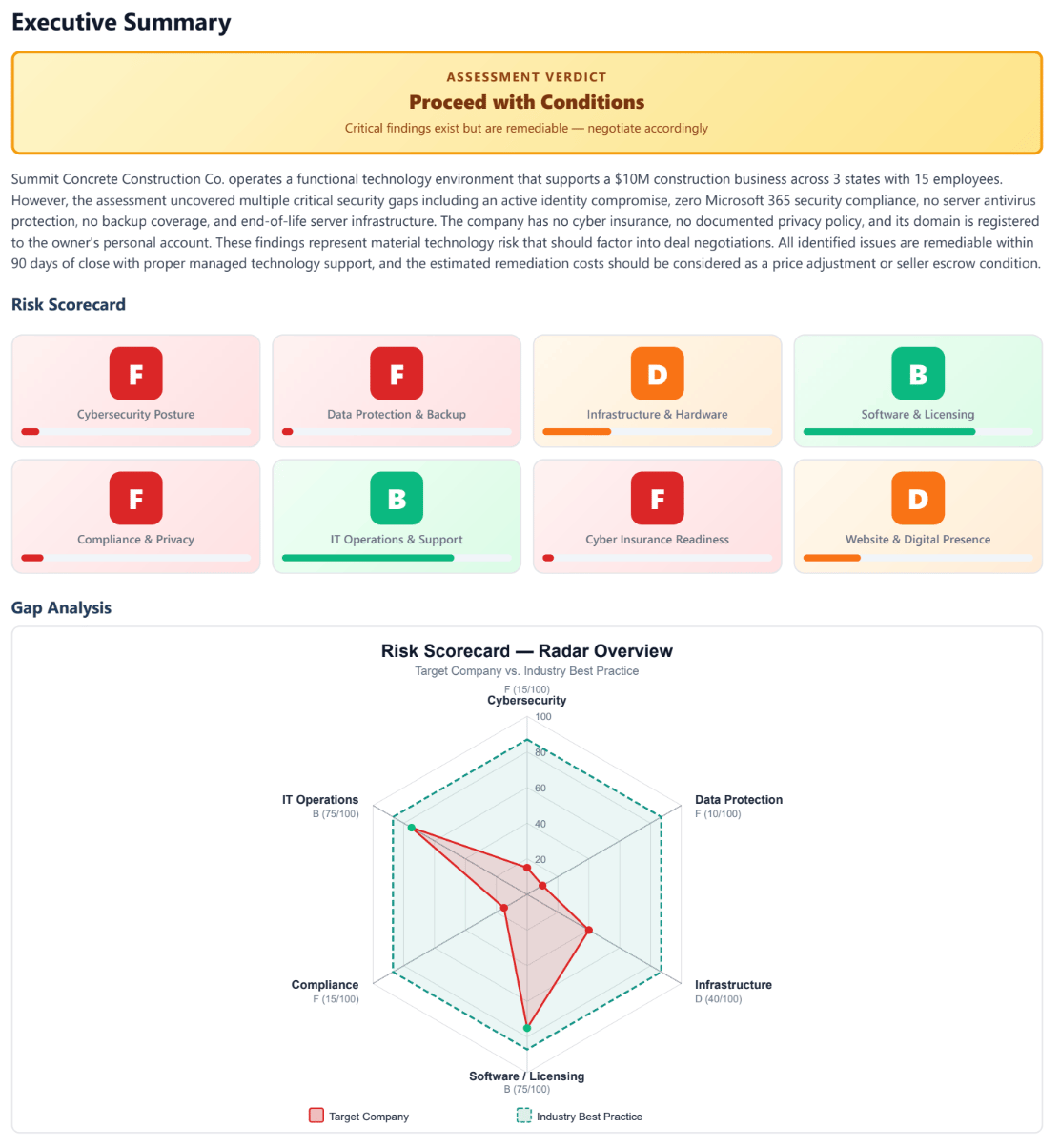
A typical QoT report runs 20 to 40 pages and includes an executive summary with a risk scorecard, a findings register with severity ratings, remediation cost estimates, and a section specifically designed for deal negotiations. The best ones include a 90-day post-close remediation roadmap so you know exactly what to fix and in what order.
Turnaround is typically 2 to 4 weeks depending on the complexity of the environment.
Preferred Data Corporation, an EBIT community member and QoT provider, shared a sample report so we get a preview of what it looks like:
The Five Findings That Change Deals
These are the patterns that show up repeatedly across SMB technology assessments. They are not edge cases. They are what a 15-employee business with a 10-year-old IT setup typically looks like under the hood.
Active Identity Compromise
What you expect: Email works. Nobody has mentioned any security incidents.
What QoTs find: Mailbox rules silently forwarding, moving, or deleting messages on multiple accounts. This is the hallmark of business email compromise. Attackers use compromised mailboxes to intercept invoices, redirect wire transfers, and impersonate executives. In construction and services businesses handling large payments, this is how wire fraud happens. Average wire fraud loss in construction ranges from $150,000 to $500,000 per incident.
Deal impact: Require the seller to confirm remediation before closing, or hold a meaningful escrow ($10,000 to $15,000) to fund incident response if the breach is more extensive than the initial scan showed.
Zero Backup Coverage
What you expect: Somebody is backing up the important stuff.
What QoTs find: No backup agent on any server. No endpoint backup. No third-party backup on cloud email or file storage. Zero of five backup categories covered. If a ransomware event occurred today, the business would have no way to recover its data. Operations across multiple locations would halt completely until systems were rebuilt from scratch, a process that typically takes 2 to 4 weeks.
Deal impact: For a $10M revenue company, even one week of downtime represents roughly $190,000 in lost revenue before you count emergency IT costs, customer impact, and potential contract penalties. This is a seller escrow or pre-close remediation item.
End-of-Life Infrastructure
What you expect: The servers are running.
What QoTs find: A domain controller running Windows Server 2016, which has not received security updates since January 2025. Every new vulnerability remains permanently unpatched. Assessments also commonly find host servers with effectively zero free disk space, meaning the next disk request crashes the domain controller and file server simultaneously.
Deal impact: Server replacement and migration typically costs $3,000 to $5,000. Not catastrophic on its own, but it should come off the purchase price since it represents deferred maintenance that accumulated under the current owner.
No Cyber Insurance (and No Way to Get It)
What you expect: The business has basic insurance coverage.
What QoTs find: No cyber insurance policy in place. And the current security posture (no MFA, no EDR, no backup, no incident response plan) means most carriers will either decline coverage entirely or quote premiums 3 to 5 times higher than a compliant business. A compliant $10M revenue company typically pays $3,000 to $8,000 per year for cyber insurance. A non-compliant one faces $15,000 to $25,000, or gets turned away.
Deal impact: Budget the remediation cost to reach insurability (typically $6,000 to $10,000 in one-time fixes) plus the annual premium as a new operating expense. Factor both into your post-close cash flow model.
Digital Identity Owned by the Seller Personally
What you expect: You are buying the company's website and email domain.
What QoTs find: The domain is registered through GoDaddy under the owner's personal account. The QuickBooks admin account is tied to the owner's personal Gmail. The Dropbox account with company files is not company-managed. If the seller departs and these accounts are not transferred, you do not actually control the company's digital presence, financial records, or file storage.
Deal impact: Require domain transfer as a closing condition. Add all critical account transfers (domain, accounting software admin, cloud storage) to the asset purchase agreement. This costs nothing to fix but is easy to miss, and the consequences are severe if you catch it after the seller walks away.
The Cumulative Effect
Here is what a real QoT assessment found on a $10M revenue, 15-employee construction company:
Category | Findings | Severity |
|---|---|---|
Cybersecurity | 5 compromised accounts, 0% M365 security compliance, 95 unpatched vulnerabilities | Critical |
Backup | Zero coverage on any system | Critical |
Infrastructure | End-of-life server, host drive at 900KB free | High |
Compliance | CIS 8.1 at 43%, NIST CSF at 0%, no cyber insurance | Critical |
Digital identity | Domain on personal account, QuickBooks on personal Gmail, shadow IT | Medium |
Total findings: 22 (5 critical, 7 high, 8 medium, 2 low).
Estimated one-time remediation: $6,500. Estimated monthly managed IT cost post-remediation: $1,650 (down from $2,000 the seller was already paying for basic support with no security, backup, or compliance included).
First-year total technology investment including all remediation: approximately $26,300 versus $24,000 the business was already spending. Essentially cost-neutral while adding comprehensive protection that did not exist before.
The technology problems were serious. The fix was not expensive. But without the assessment, the buyer would have inherited all of it blind.
One more thing worth noting: QoT findings can affect your SBA financing. If your lender discovers material technology risk during underwriting (active breach, no cyber insurance, no disaster recovery), it can complicate or delay closing. Running the QoT early in diligence means you surface and address issues before they become lending problems.
When to Order a QoT (and What Level You Need)
The level of assessment depends on the deal. Here is how to think about it.
Always order a QoT when:
The business handles sensitive data. Customer financial records, health information, employee SSNs, payment processing. A breach of this data creates notification obligations and potential lawsuits that land on you as the new owner.
The business has on-premises servers and a local network. This is where the serious findings live. Cloud-only businesses have a different (usually smaller) risk profile.
You plan to scale post-close. If your value creation thesis depends on adding locations, employees, or capabilities, you need to know whether the technology can handle it or whether it will cap your growth.
The owner or controller doubles as the IT person. This is a single point of failure. If that person leaves post-close and nothing is documented, you are starting from scratch.
The company does government contract work. NIST 800-171 compliance requirements can disqualify the business from federal contracts if the security posture is too weak.
A lighter-touch scan may be sufficient when:
The business is entirely cloud-based with no on-premises infrastructure. The company already has a managed IT provider with documented security controls. The deal is small enough that the cost of a full QoT is disproportionate to deal value.
Decision framework: If the business has servers, a network, and more than 10 employees, a QoT is almost always worth it. The cost (typically $2,500 to $10,000 for a small business) is a fraction of the risk you are underwriting without one.
How QoT Findings Translate to Negotiation Leverage
This is the section your attorney needs to see. A well-structured QoT report categorizes every finding into one of four deal actions:
Seller remediation pre-close. Items the seller must fix before you close. Examples: deploy antivirus on servers, establish backup coverage, transfer the domain to a company-controlled account, resolve the disk space crisis that could crash the infrastructure. These are not negotiable. You should not inherit an active security compromise.
Seller escrow. Items that require investigation or remediation that cannot be verified before close. Examples: identity compromise incident response, M365 security hardening, risky user investigation. Hold $10,000 to $15,000 in escrow to fund this work after closing.
Purchase price reduction. Deferred maintenance that accumulated under the current owner. Examples: end-of-life server replacement, vulnerability patching, disk encryption deployment. These represent costs the seller should have incurred but did not. Request $6,000 to $8,000 off the purchase price.
Acquirer accepts risk. Items the buyer will handle post-close as part of normal operations. Examples: AD password policy modernization, compliance framework alignment, website performance optimization. These are improvements, not deficiencies.
The total across all four categories gives you a specific, documented dollar amount to bring to the negotiation. Not "we think there might be IT issues." A findings register with severity ratings, remediation estimates, and recommended deal actions.
The 90-Day Post-Close Playbook
If the QoT is the diagnostic, the 90-day plan is the treatment. Here is what a structured remediation looks like:
Days 1 to 30: Stabilize. Deploy endpoint detection across all servers and workstations. Enforce multi-factor authentication on all accounts. Remediate any active identity compromises. Establish backup coverage. Address any infrastructure emergencies (disk space, end-of-life systems).
Days 31 to 60: Standardize. Deploy remote monitoring and management across all endpoints. Establish a patching program. Set up encrypted VPN for remote workers. Launch security awareness training. Begin server migrations and AD cleanup. Document the full IT environment so you are not dependent on one person's memory.
Days 61 to 90: Scale. Virtual CIO engagement to align the technology roadmap with your growth plans. AI readiness assessment to identify processes ripe for automation. Compliance framework alignment. Obtain cyber insurance quotes now that the security posture supports reasonable premiums.
The goal is simple: go from high-risk to managed-risk in 90 days, at a cost that is typically comparable to what the business was already spending on IT support that was not actually protecting it.
If you have a deal in diligence right now, forward them the negotiation leverage section above. It could save them five figures in post-close surprises.
Finding the Right QoT Partner
Technology due diligence for SMB acquisitions is a relatively new category. Most IT firms focus on break-fix support or enterprise consulting. You want a partner who understands deal timelines, speaks the language of acquisition diligence, and produces reports that work at the negotiation table.
What to look for: A report structured for deal negotiations, not just an IT audit. Clear severity ratings with estimated remediation costs. A findings register your attorney can use directly. Experience with SMB acquisitions specifically. Willingness to execute the remediation they recommend, not just hand you a PDF and disappear.
Preferred Data Corporation offers QoT assessments designed specifically for acquisition diligence. They have been in business for 37+ years with an A+ BBB rating and their reports include the negotiation leverage section and 90-day remediation roadmap described in this article. They also offer a free outside-in scan before your LOI (domain health, breach exposure, tech stack identification) that requires no site access and no cost. If you want to see how they approach the topic, check out their webinar here.
Questions to ask any QoT provider:
Can you complete the assessment within my diligence timeline (typically 2 to 4 weeks)? Do you produce a negotiation leverage section with dollar estimates I can take to the seller? Will you execute the remediation post-close, or is this just a report? Can I see a sample report before I commit?
Key Takeaways
A QoT is the technology version of a QoE. It separates what the seller says about their IT from what the evidence shows. The same rigor you apply to financial diligence should apply to technology.
The most common findings are not exotic. Compromised email accounts, zero backup, end-of-life servers, no cyber insurance, and digital assets registered to the seller's personal accounts. These show up in the majority of SMB assessments.
Remediation is usually cheaper than you think. The construction company example had 22 findings including 5 critical, and the total first-year remediation cost was roughly $26,000. The risk of not knowing was orders of magnitude higher.
Use findings as negotiation leverage. A structured QoT report gives you specific dollar amounts for price reductions, escrow holdbacks, and seller remediation conditions. Your attorney can use the findings register directly in deal negotiations.
The 90-day post-close plan matters as much as the assessment. Knowing what is wrong is only half the value. Having a structured plan to fix it in the first 90 days of ownership is what actually protects your investment.
Technology risk is deal risk. An uninsured, unprotected business is one ransomware attack away from weeks of downtime and six figures in losses. That exposure should be quantified and priced into the deal, not discovered after you sign.
Disclaimer: This guide is for educational purposes only and does not constitute legal, financial, tax, or investment advice. Business acquisitions involve significant risks, and outcomes can vary widely based on individual circumstances. Always consult with qualified professionals including attorneys, CPAs, and financial advisors before making acquisition decisions. The EBIT Community does not guarantee the accuracy of information provided or the success of any acquisition strategy. Past performance and examples do not guarantee future results.

